
Exploit released for Atlassian Confluence RCE bug, patch now

Evidence-of-principle exploits for the actively exploited critical CVE-2022-26134 vulnerability impacting Atlassian Confluence and Info Middle servers have been extensively launched this weekend.
The vulnerability tracked as CVE-2022-26134 is a critical unauthenticated, remote code execution vulnerability exploited by OGNL injection and impacts all Atlassian Confluence and Details Middle 2016 servers soon after variation 1.3..
Profitable exploitation makes it possible for unauthenticated, remote attackers to generate new admin accounts, execute instructions, and in the long run get more than the server.
The vulnerability was disclosed final week after Volexity found out it was used by numerous threat actors in attacks. At the time, a patch was not obtainable, and Atlassian recommended admins to take servers offline or block them from currently being accessible from the Net.
On Friday, Atlassian released safety updates to take care of the vulnerability just as attacks escalated in the wild.
Confluence exploits publicly launched
Friday afternoon, a evidence-of-strategy exploit for the Atlassian Confluence vulnerability was publicly posted. The exploit quickly unfold broadly on line more than the weekend, with researchers sharing examples on Twitter of how trivial it was to exploit.
Yesterday afternoon, Andrew Morris, the CEO of cybersecurity business GreyNoise, tweeted that they had begun to see 23 exceptional IP addresses exploiting the Atlassian vulnerabilities.
Now, GreyNoise studies that the variety of one of a kind IP addresses trying to exploit this vulnerability has developed virtually 10 situations, to 211 distinctive IP addresses.
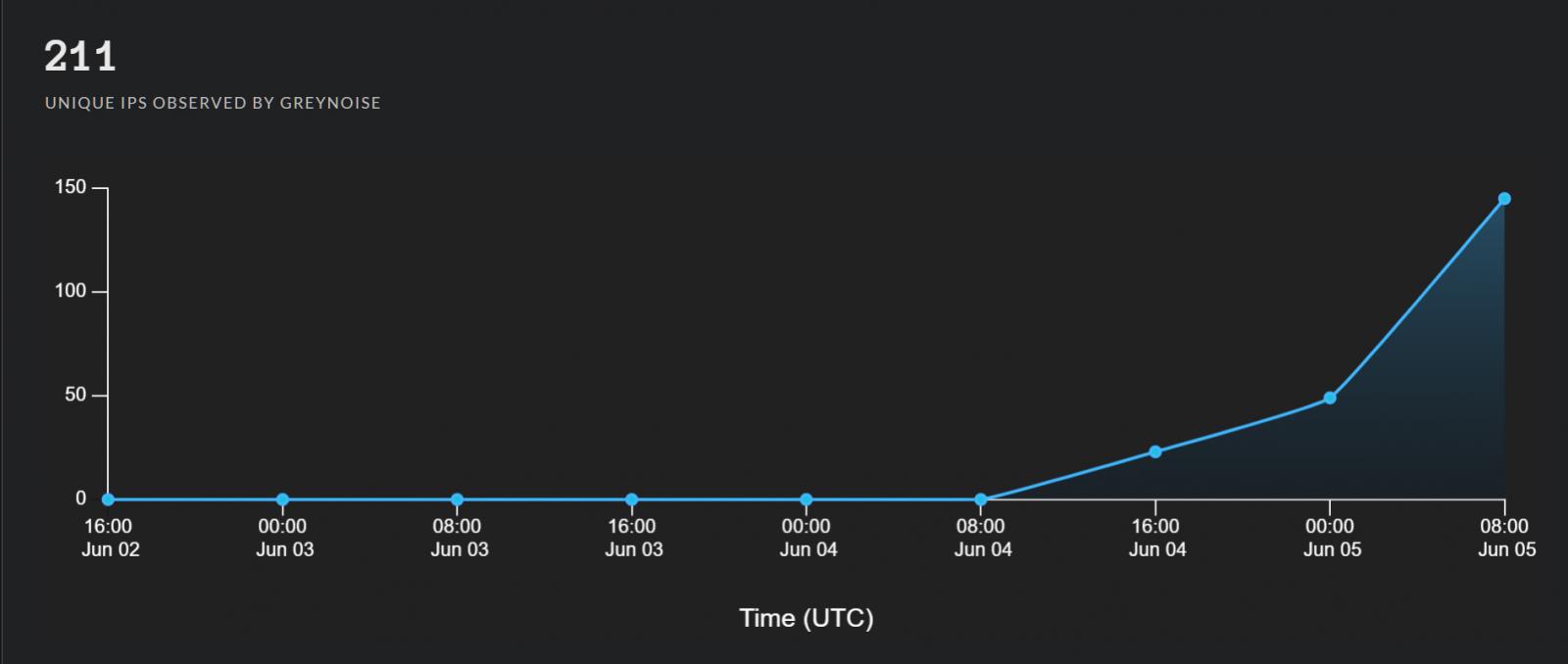
Source: GreyNoise
Confluence exploits posted on-line demonstrate how to create new admin accounts, power DNS requests, assemble information and facts, and make reverse shells.
Patch your Confluence servers now
If you haven’t however patched the stability vulnerability in your Confluence or Knowledge Middle servers, you must do so instantly ahead of danger actors compromise them.
“Produced versions 7.4.17, 7.13.7, 7.14.3, 7.15.2, 7.16.4, 7.17.4 and 7.18.1 which include a fix for this challenge,” clarifies the Atlassian advisory.
If for some rationale, you are not able to patch your servers immediately, Atlassian has provided mitigations for Confluence 7.. by version 7.18..
As Confluence servers are an attractive target for first access to a corporate network, gadgets should really be current promptly, mitigated, or taken offline.
Not executing so will in the long run lead to additional considerable attacks, which includes ransomware deployment and details theft.
